Do you know that if your Conditional Access (CA) policies were poorly designed, your users can evade them with just a couple of clicks? And the title of this post is not a “clickbait”, let me show you how it can be done, why this is happening and how to avoid this.
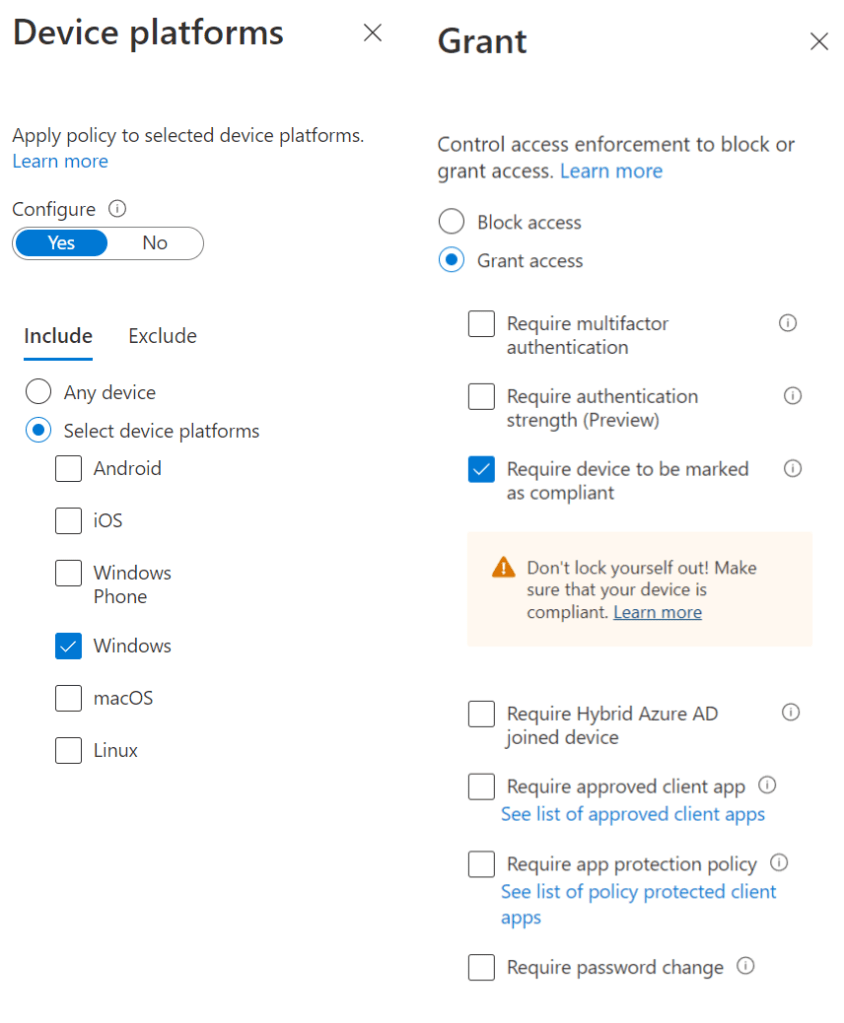
First, I’m going to create a policy that requires a compliant Windows device. Pretty standard policy.
Now, if a user tries to access the application from a not-compliant Windows device he is getting a standard message.
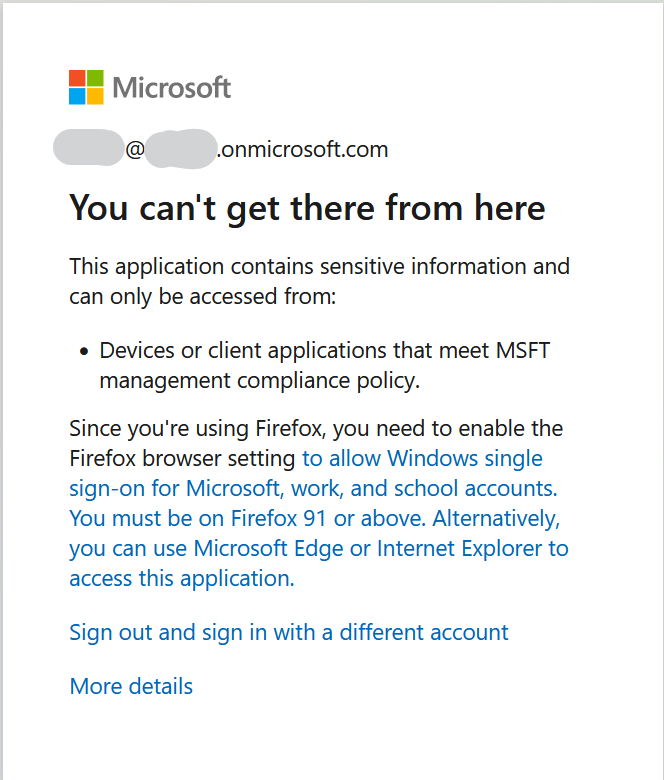
So, we are protected and everything is good? Unfortunately not, because our fence has a lot of holes. And here is a question that might help us to understand why.
How Azure AD detects OS?
I don’t recall this information in Microsoft docs several years ago, but now they do have this call out in the doc:
The information used to calculate the device platform comes from unverified sources such as user agent strings that can be changed.
In reality, it is a bit more complicated, since there are other sources of information like information from ADAL/MSAL in the case of apps and device information from Intune. But User-Agent is still used.
Now we can check what is going to happen in case of a changed User-Agent.
Let’s hack Conditional Access policy!
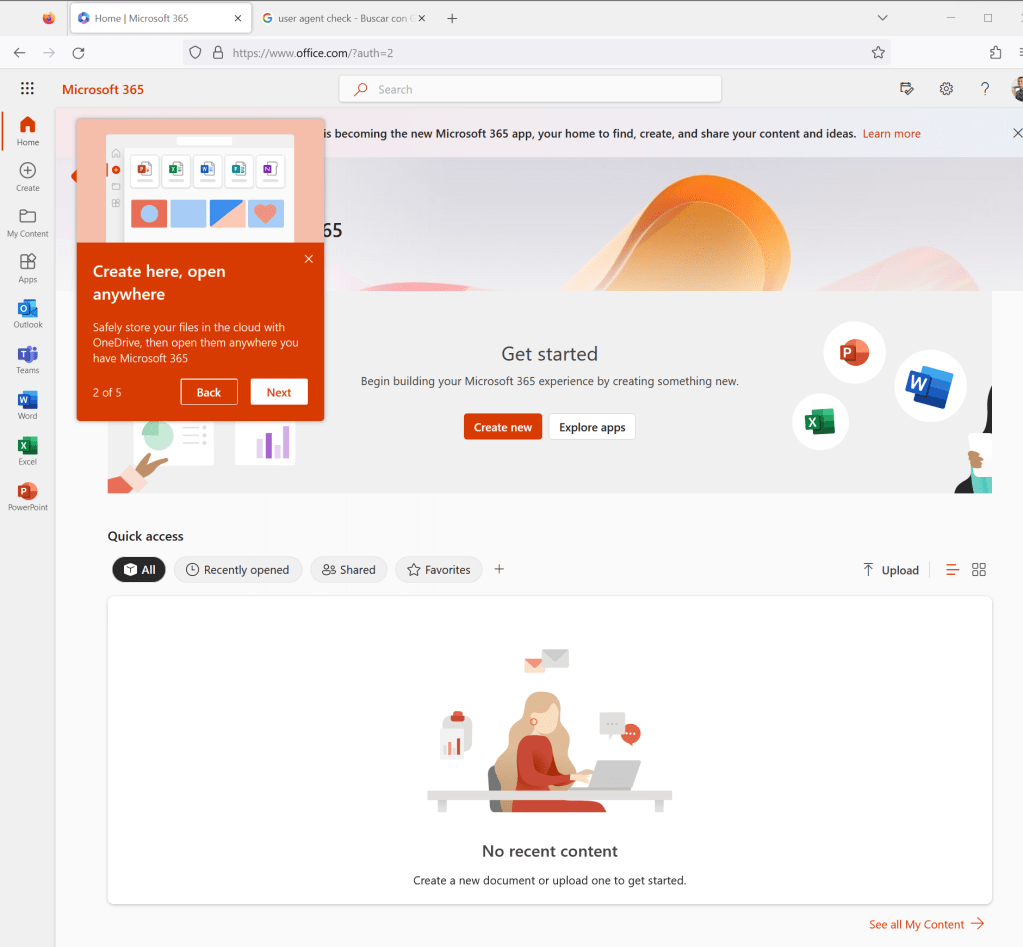
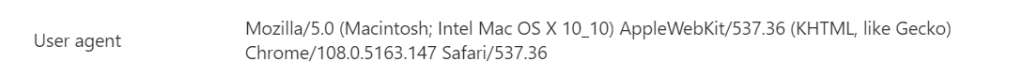
The easiest way to change User-Agent now is by using a browser extension. In my case, I changed it from Windows to MacOS.

And now I can get in without any problems.
To understand what is going on, we need to check Sign-In logs. In the first sign-in attempt Conditional Access policy blocked the connection.
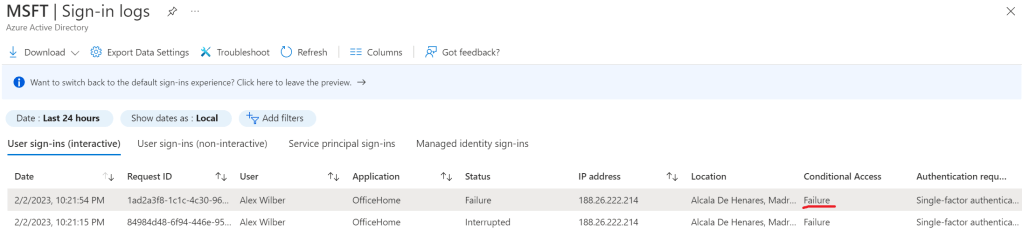
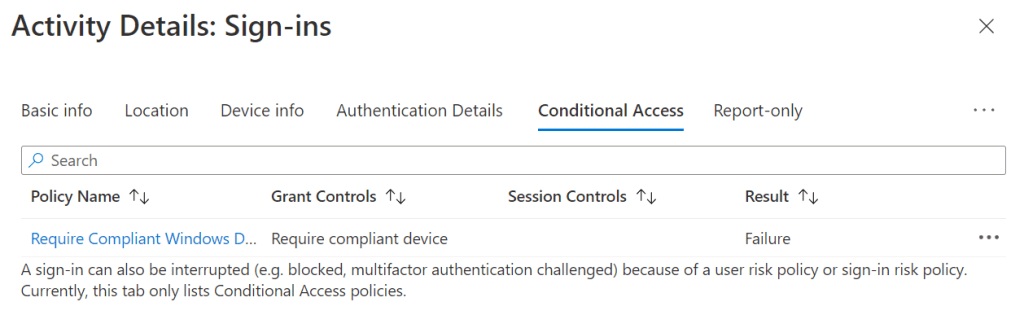
But what is happening in successful login?

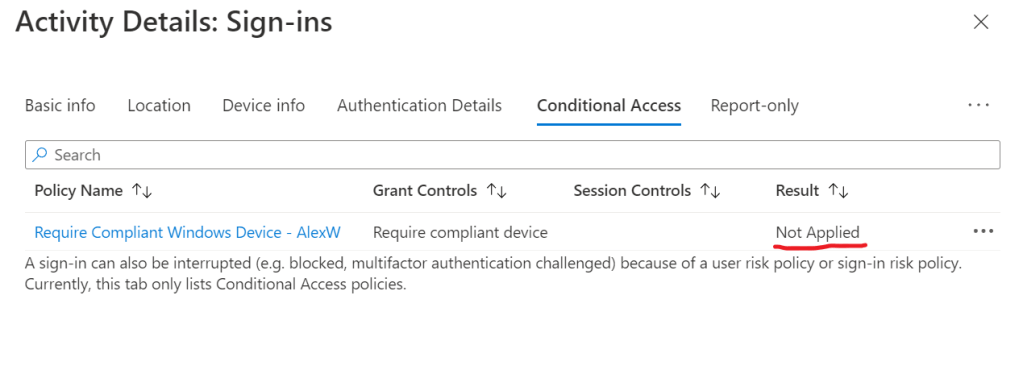
As you can see, Conditional Access policy just was not applied. And if we look in Device info we will see, that platform was detected as macOS.
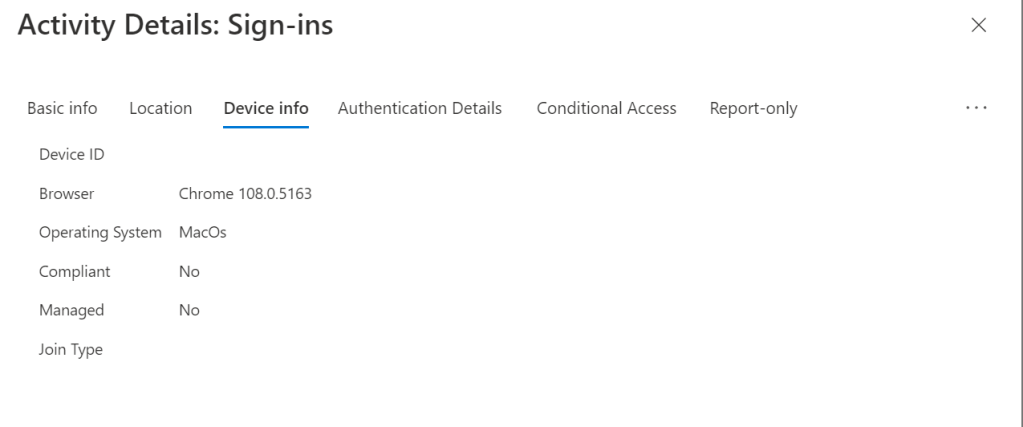
And here is our User-Agent.
But no one is going to change User-Agent!
Well, I can argue with this statement, but the change of User-Agent was aimed just to show you that Device Platform is good for scoping specific policies, but you should cover all platforms in your policies because you have no idea of what platforms your users are going to use.
Conditional Access policy is just a tool and by creating a set of policies with holes, unfortunately, you are not improving security.
How to fix it?
Obviously, by having another Conditional Access policy.
For example, let’s assume that we have the following platforms managed by Intune – Windows, iOS, Android and macOS. If any of these devices are going to connect to apps, Azure AD will be able to get more information about device from Intune, or force device to be enrolled (or get App Protection policies). But what we should do with other platforms?
Easy, block them.
Step-by-step guide can be found in Microsoft docs.
Summary
I am always saying that Conditional Access policies are not a silver bullet. You have to analyze your environment, identify threats and mitigate them. Do not rush to start creating random policies and try to think about a holistic approach.
I like this phrase from US Navy Seals: “Slow is smooth, smooth is fast”. Think about what you are doing and do not fall into action-mode narrow vision.
I am preparing a post about how to monitor your Conditional Access policies, including the detection of possible evasions. Stay tuned!